Understanding the Internet, Part 3: Practical Applications

After explaining the mysteries of IP addresses and how domain names work, Jacques Morrisseau explains how to take advantage of this knowledge on a daily basis.
[Understanding the Internet, Part 1: IP addressing and ports.]
[Understanding the Internet, Part 2: Domain names.]
Test your network connection like a pro!
Let’s review the tests from our first part and add a third step:
- Step 1 – Test access to your gateway.
- In the previously opened CMD window, type:
- ping 192.168.1.1 (your router’s address).
- If you see a line saying that 4 packets were sent and received, the test was successful.
- Otherwise, there is a connectivity problem with your router.
- In the previously opened CMD window, type:
- Step 2 – Test Internet access.
- ping 8.8.8.8.
- This is a Google DNS service that also responds to pings.
- If it answers, your Internet access works.
- Step 3 – Test the DNS resolution.
- ping google.ca.
- The command informs you of the IP address associated with this domain name and pings to it.
- If the operation fails, it means that your name resolution service is malfunctioning.
If the ping test to a domain name is successful as the test to a numerical address, your Internet service is in principle fully functional. If you can’t access the Internet with your browser, there is certainly a problem with it. There are several potential sources of problems, but they alone could be the subject of a whole series of articles.
Spot phishing attempts like a pro!
When you receive an email, the first thing to check is the “From” field or the sender. It is highly possible that a malicious person may try to pretend to be someone else, such as your bank. In this case, the “From” could look like this:
Big Bank <thingamajig@doohickey.com>
In this example, “Big Bank” will be called the label and “doohickey@thingamajig.com” will be the real email address. As the label is totally different from the real email address, it is already a very good indicator of a phishing attempt.
Generally, you will find a link to click in this email. In this case, take your mouse and hover over the link without clicking. Most of the time, you will see a URL address that has no connection to the alleged company.
Often, these compromised sites are small PHP websites, and you will have URLs like this:
http://www.doohickey.com/index.html/compromised_stuff.php
Real-life case study
And again, you must always be cautious, because some phishing attempts are very well executed. Some hackers will go so far as buying a similar domain name to that of the targeted provider. Recently, I received an email claiming to come from my bank (Royal Bank of Canada) which was extremely well done. Here is a screenshot:
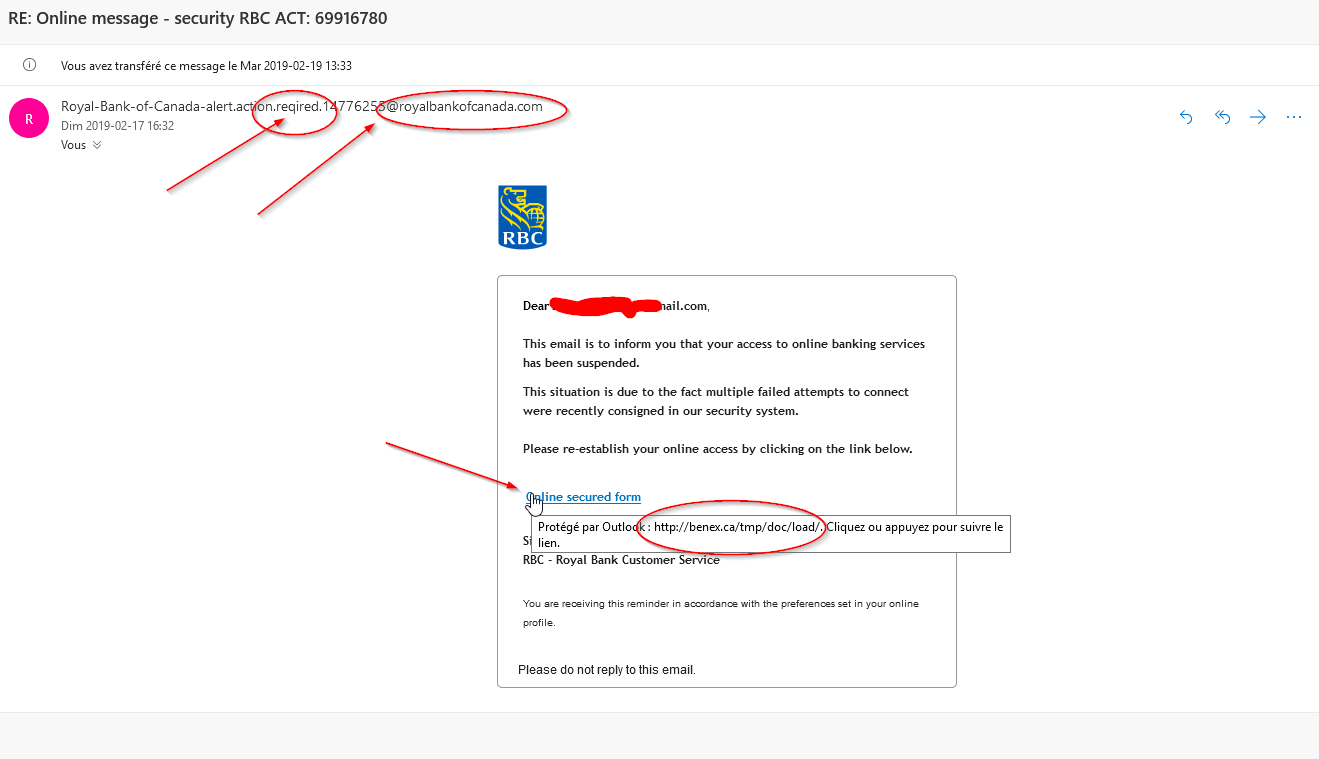
Please note the following clues:
- Similar domain name:
- The official website of my bank is rbc.com.
- The email came from the domain royalbankofcanada.com.
- If you type these two domain names into a browser, you will quickly be able to check which one is fraudulent (see below for a more “technical” verification tool).
- Incorrect spelling:
- For some unknown reason, perhaps because—insert your favourite scapegoats and biases here—, hackers have a lot of difficulty with grammar and spelling.
- In our example, we can see a gross error: “required” is written “reqired”.
- If you look at the destination of the link “Online secured form”:
- When hovering over the link, the box below reveals that the actual destination is the URL “http://*****.ca/tmp/doc/load/”.
- Obviously, it has nothing to do with rbc.com.
Domain name checks
There are several “whois” type services to verify domain names. One of them is whois.com. Here is the information provided by this service for royalbankofcanada.com and rbc.com:
Whois for “royalbankofcanada.com”
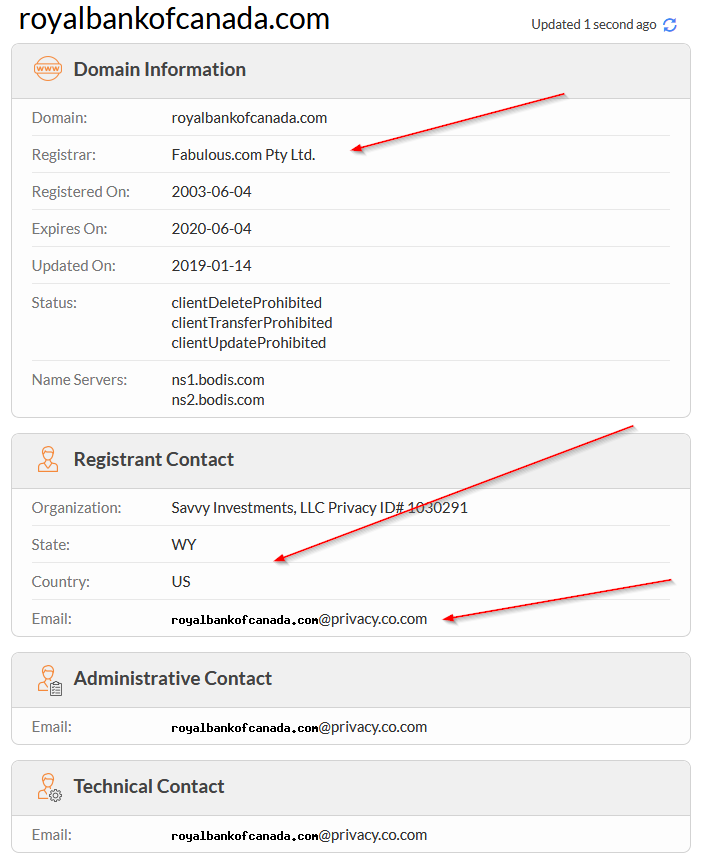
We’re talking about a supposed bank, however:
- The registrar is called “Fabulous.com”, not quite serious.
- A Canadian bank registered in Wyoming is surprising.
- The emails declared are anonymous addresses:
- An anonymous email address often contains the word “privacy” somewhere.
- The email addresses should have been “@royalbankofcanada.com”.
- A legitimate company of the scale of a large bank will provide several email addresses to contact in the event of a problem as well as a physical postal address and phone numbers.
Whois for “rbc.com”
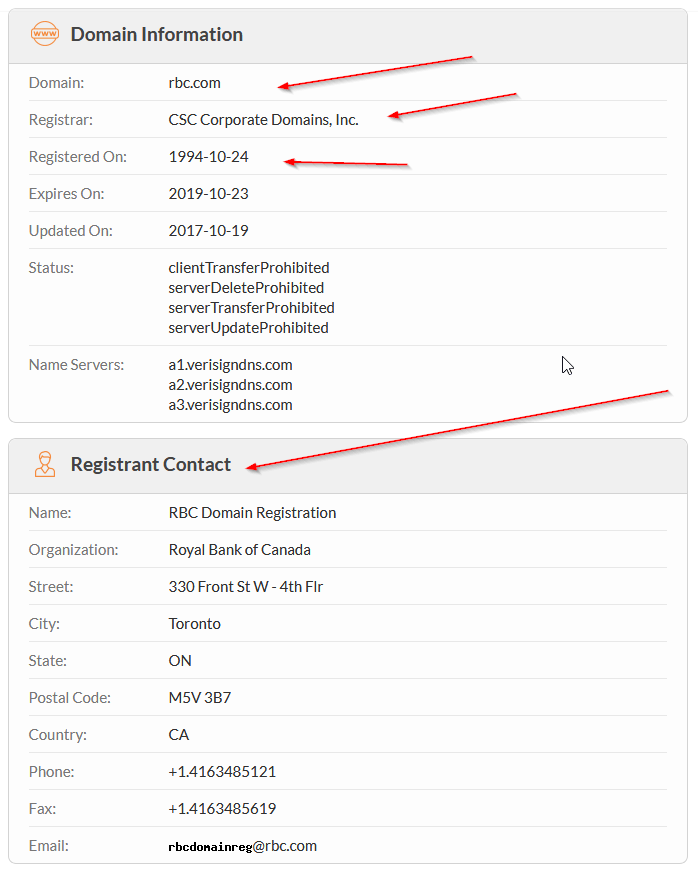
As you can see here, there is a lot more information, including real email addresses, a physical address and phone and fax numbers. All this, of course, in the country where the company is supposed to operate.
However, something more insidious happened to me: I also received an email from rbc.ca (note the Top Level Domain in “.ca” and not in “.com”) and after checking with the whois service, the domain name was registered to an apartment address in Toronto.
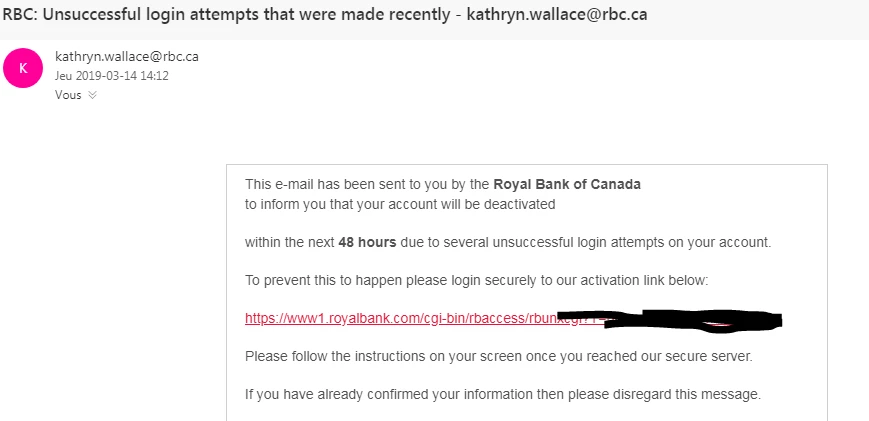
Unfortunately, fraudulent domain names attempting to scam RBC clients have been around for a long time and despite my emails on this subject, my bank does not seem to take this seriously or consider its clients’ safety as a priority. It is probably a little more complicated to manage the problem at the legal level with a domain name registered in Wyoming, but the address in “.ca” should have been taken care of long ago. This domain name has been in use since October 2000!
Check the real destination of a link!
Here is a link to our website:
If you click on it, you will go without surprise on the home page of our site. Now, look at the following link:
If you look at this link without paying attention, you might start salivating and daydreaming about potatoes, but if you click on it, you will realize that it’s actually a fraudulent attempt to generate clicks to a site without any link to potatoes (ours in this case).
A very easy way to check the validity of a link in your browser is to simply move the mouse pointer over the link, without clicking on it. At the bottom left of the navigation window, you should normally see an indication of the actual destination of this link.
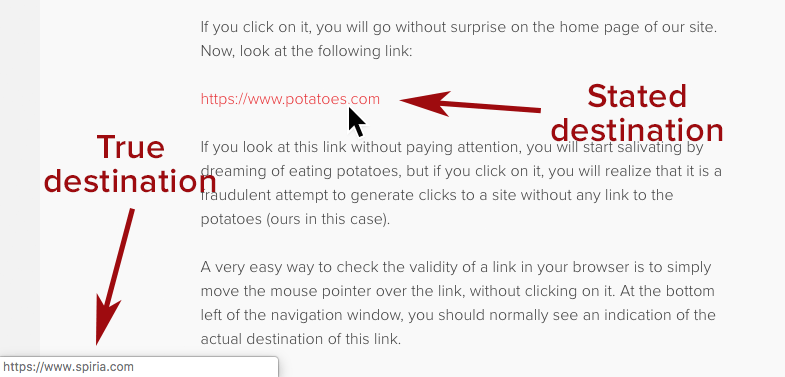
Hyperlinks on text are the basis of the web—they allow you to point to a specific resource with clear wording rather than a URL that isn’t necessarily meaningful—however they can be diverted from their normal use by associating misleading link text with a destination that has nothing to do with it. For example: “I like potatoes.”
Check the legitimacy of DNS and emails like a pro!
As briefly mentioned, online services can be used to verify the legitimacy of a website. In general, if you are looking for the web address of any organization, a simple search with its name on Google should return the main website in the first results. Since SEO on Google costs time and money, it is highly unlikely that a hacker will invest the necessary sums to divert traffic to a pirated site under his control. It is possible that a company has several domain names to its credit, a simple check in whois.com will allow you to check their validity or confirm your suspicions, if necessary.
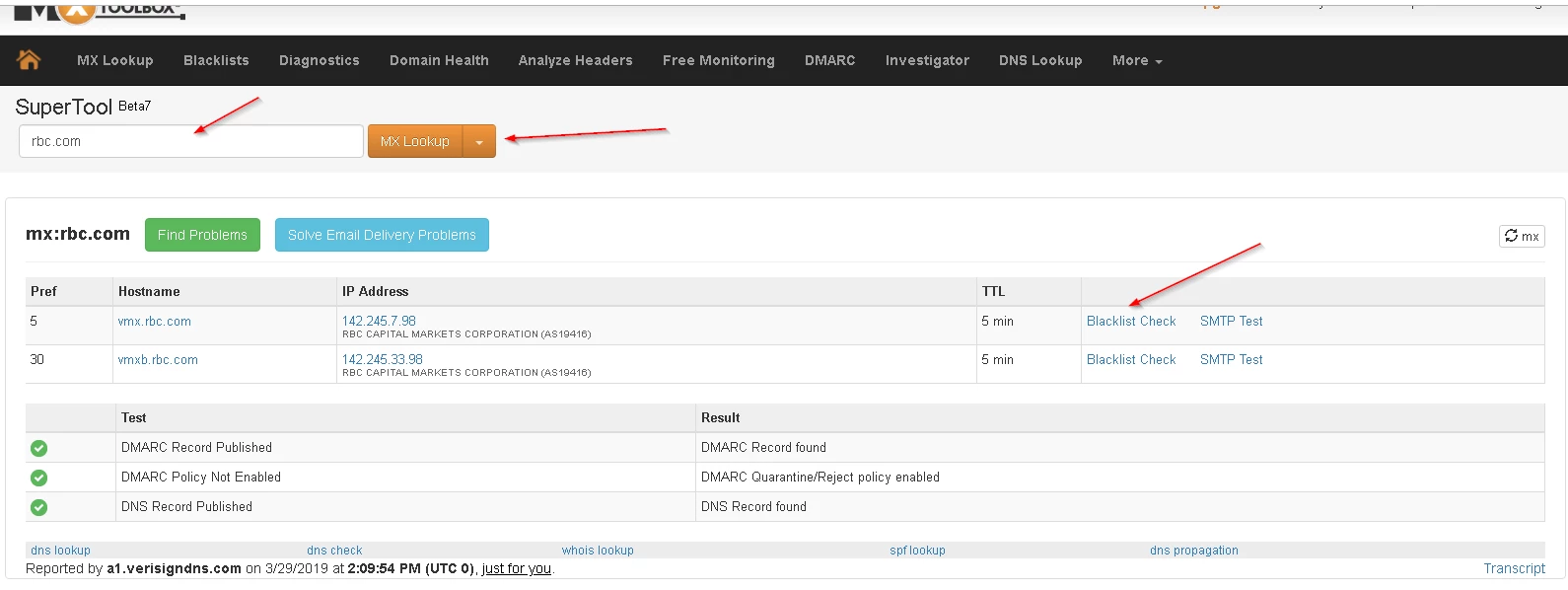
If you have any doubts about the domain when sending an email or if you want to check if you have an incorrectly configured or worse, blacklisted service, you can use the service MxToolbox. Continuing with the example of my bank, here are some basic functions you can use.
In the following screenshot, you can see that there are MX records associated with rbc.com. If you are doing the exercise for one of your domain names, you can check if it’s featured on a known blacklist.
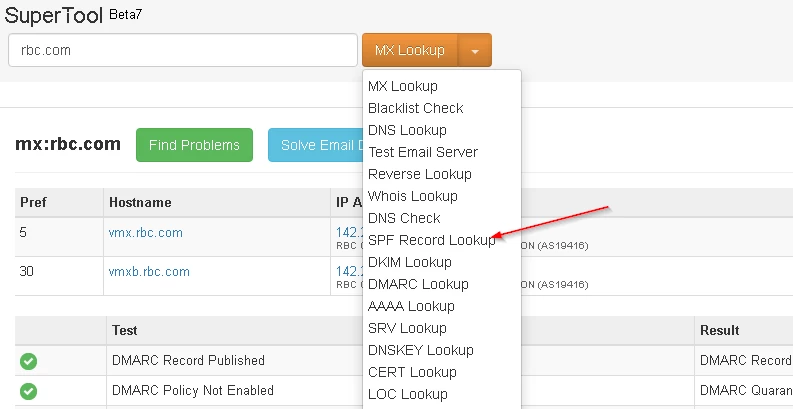
Further analysis can be done by selecting “SPF Record Lookup.” The SPF is used to identify the servers authorized to send email for the specified domain name:
In the case of rbc.com, this is what it looks like. Normally, there should be at least one entry.
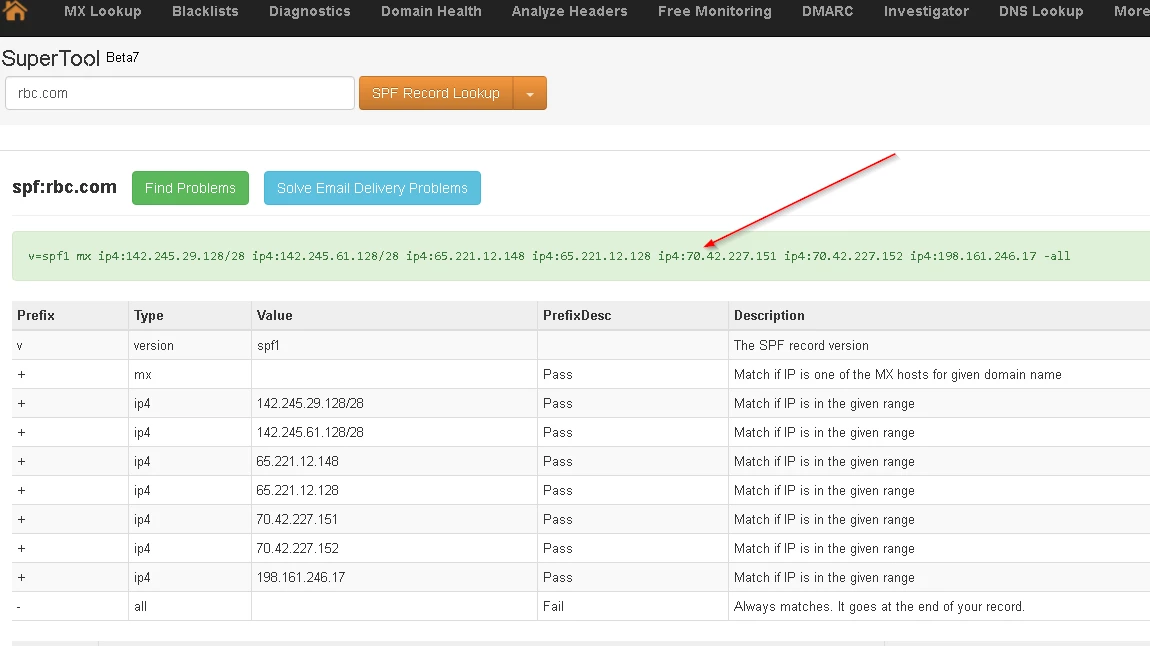
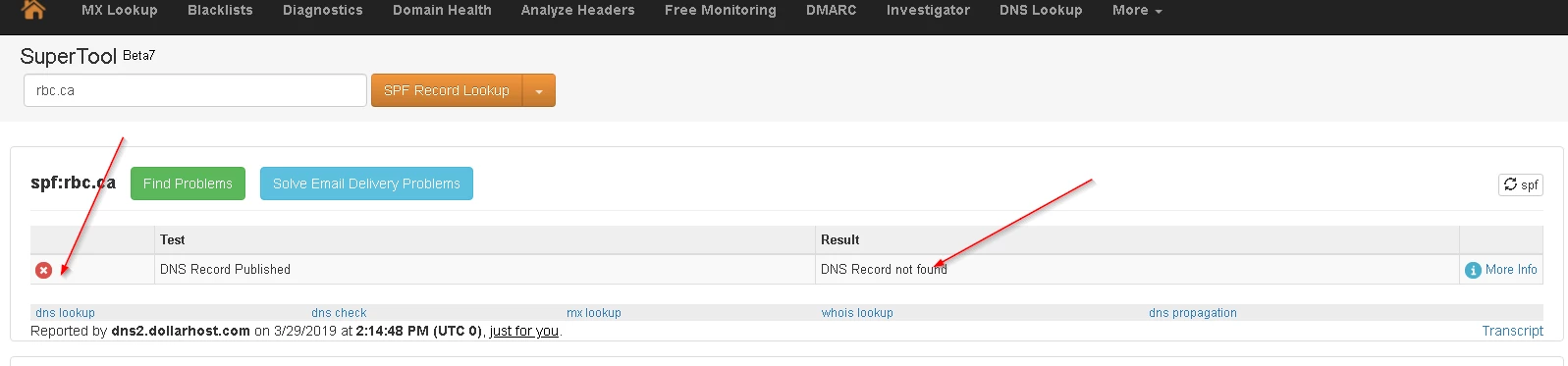
In the case of a fraudulent site, we generally do not even bother to enter an SPF, as you see for rbc.ca:
If you do not have an SPF associated with your domain name, your email messages are generally more likely to be considered spam. If this is your case, you should quickly remedy the situation.
In Conclusion
That concludes my basic introduction to the Internet. There are many sites, books and courses on this vast subject and you would not have enough of a lifetime to consult them all. The important thing is to understand the basics and go deeper according to your needs. In this regard, here are some additional references on Wikipedia to get you started:
